Threat Watch
Collaborate to swiftly evaluate and enhance your team's cybersecurity health with Threat Watch's comprehensive scan.
Visit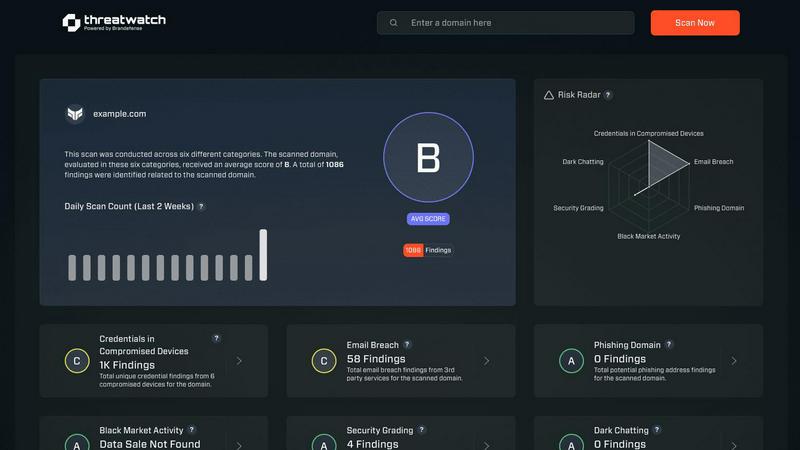
About Threat Watch
Threat Watch is a cutting-edge unified cybersecurity intelligence platform designed to support and enhance the efforts of your entire security team. It provides a clear, actionable perspective on your organization’s digital risk posture, empowering teams to work collaboratively in safeguarding their assets. This platform serves as a central hub that continuously monitors and analyzes external assets, vulnerabilities, and exposures across various domains, including the clear, deep, and dark web. By aggregating and synthesizing data from these vast sources, Threat Watch generates a comprehensive "cyber health" score. This enables organizations to shift from a reactive approach to a proactive stance in risk management. Tailored for IT leaders, security analysts, and risk management professionals, Threat Watch consolidates data on compromised credentials, devices, phishing campaigns, and dark web threats into one real-time source of truth. Its main value proposition is its ability to foster synergy between different functional teams—from IT operations to executive leadership—ensuring a unified approach to countering threats effectively.
Features of Threat Watch
Comprehensive Cyber Health Scoring
Threat Watch delivers a holistic "cyber health" score that encapsulates your organization's risk posture in real-time, allowing teams to prioritize their security efforts based on data-driven insights.
Real-Time Threat Monitoring
With continuous analysis of assets and vulnerabilities across the internet, Threat Watch provides real-time updates on potential threats, ensuring your security team is always informed and ready to respond swiftly.
Dark Web Surveillance
Threat Watch actively monitors the dark web for leaks and breaches related to your organization, delivering timely alerts that help mitigate risks associated with compromised credentials and sensitive data exposure.
Collaborative Dashboard
The platform features a user-friendly dashboard that promotes collaboration among team members. This centralized view allows IT, security, and executive teams to align their strategies and responses based on a unified understanding of threats.
Use Cases of Threat Watch
Proactive Risk Management
Organizations can utilize Threat Watch to assess their cyber health continuously, enabling proactive measures that can be taken before threats escalate into significant incidents.
Incident Response Coordination
In the event of a detected security breach, Threat Watch facilitates coordinated incident response by providing real-time data and insights, ensuring that all relevant team members are informed and can act swiftly.
Compliance and Reporting
Threat Watch aids organizations in maintaining compliance with industry regulations by providing detailed reports on security posture and breach incidents, making it easier to demonstrate due diligence to stakeholders.
Security Awareness Training
By leveraging the insights from Threat Watch, security teams can educate employees about emerging threats such as phishing attacks and compromised credentials, fostering a culture of awareness and vigilance within the organization.
Frequently Asked Questions
What types of data does Threat Watch analyze?
Threat Watch analyzes a wide range of data, including information from the clear web, deep web, and dark web. It focuses on external assets, vulnerabilities, and exposures to give a comprehensive view of your organization’s digital risk environment.
How frequently is the information updated on Threat Watch?
Threat Watch updates its information in real-time, ensuring that your security team has access to the latest intelligence on threats, vulnerabilities, and compromised assets as they arise.
Who can benefit from using Threat Watch?
Threat Watch is designed for IT leaders, security analysts, and risk management professionals. Its collaborative nature makes it ideal for teams that need to synchronize their efforts in mitigating risks and responding to threats.
Is Threat Watch suitable for small businesses?
Yes, Threat Watch is suitable for organizations of all sizes. Its comprehensive capabilities allow small businesses to leverage powerful cybersecurity intelligence without the need for extensive resources, enhancing their overall security posture.
Explore more in this category:
Similar to Threat Watch
Decker
Decker is your team's operating system for building review-ready deliverables and earning from your expertise together.
FX Radar
FX Radar leverages AI to deliver real-time market insights and analysis, empowering traders to identify actionable signals swiftly.
AI Business Name Generator
Let our AI Business Name Generator work with you to create unique, brandable names that set your startup or domain apart.
Opal44
Opal44 simplifies your GA4 website traffic data with AI insights in plain English for smarter, actionable decisions.
Fusedash
Fusedash turns your team's data into clear dashboards so everyone can act on insights together.
finban
finban empowers you to plan liquidity confidently, ensuring informed decisions on hiring, taxes, and investments.
aVenture
aVenture is a collaborative AI platform for comprehensive startup research, competitor analysis, and investor tracking.