iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
iGPT transforms messy email data into secure, actionable insights for teams, enhancing workflow efficiency and.
Last updated: March 1, 2026
Threat Watch
Collaborate to swiftly evaluate and enhance your team's cybersecurity health with Threat Watch's comprehensive scan.
Last updated: March 1, 2026
Visual Comparison
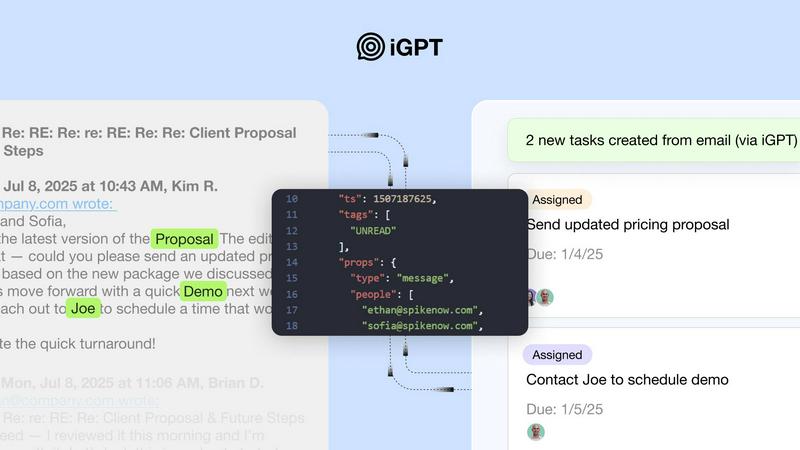
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
With iGPT, teams experience immediate integration through an SDK and a live playground that facilitates quick testing of requests and responses. This seamless onboarding process allows developers to engage with the API right away, ensuring that their systems are up and running in no time.
Deep Email Indexing
iGPT automatically indexes emails and attachment data, allowing for comprehensive retrieval of information. This deep indexing capability ensures that users can access relevant context and data without the need for manual intervention, enhancing the efficiency of workflows.
Unified Endpoint
The API provides a single, unified endpoint that performs retrieval, context shaping, and reasoning in one streamlined pipeline. This eliminates the need for complex multi-endpoint setups, allowing teams to make simple requests that yield rich, contextual responses.
Real-time Ingestion
iGPT boasts real-time ingestion capabilities, instantly indexing new messages and attachments as they arrive. This feature ensures that teams are always working with the most current data, which is vital for maintaining productivity and informed decision-making.
Threat Watch
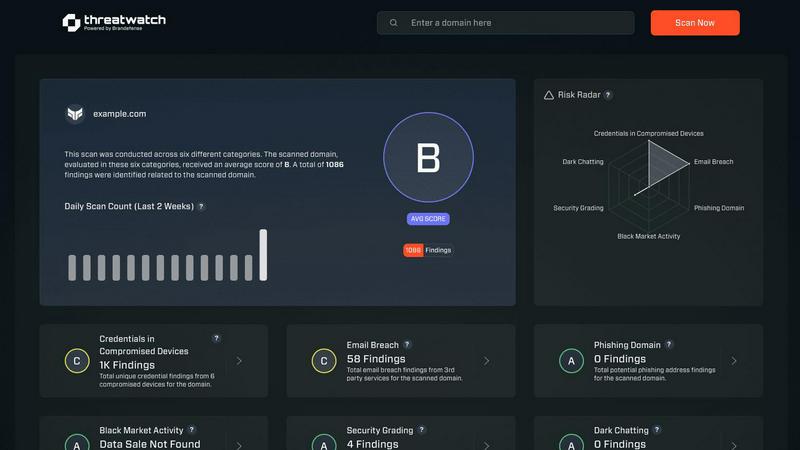
Comprehensive Cyber Health Scoring
Threat Watch delivers a holistic "cyber health" score that encapsulates your organization's risk posture in real-time, allowing teams to prioritize their security efforts based on data-driven insights.
Real-Time Threat Monitoring
With continuous analysis of assets and vulnerabilities across the internet, Threat Watch provides real-time updates on potential threats, ensuring your security team is always informed and ready to respond swiftly.
Dark Web Surveillance
Threat Watch actively monitors the dark web for leaks and breaches related to your organization, delivering timely alerts that help mitigate risks associated with compromised credentials and sensitive data exposure.
Collaborative Dashboard
The platform features a user-friendly dashboard that promotes collaboration among team members. This centralized view allows IT, security, and executive teams to align their strategies and responses based on a unified understanding of threats.
Use Cases
iGPT
Email Assistants
Teams can develop intelligent email assistants that draft responses, prioritize messages, and take action based on full context. By leveraging iGPT, organizations can enhance their email management processes, thus improving overall efficiency.
Workflow Automation
iGPT allows organizations to convert email threads into actionable tasks, deadlines, and approvals. This automation capability helps in tracking progress and ensuring that important items are not overlooked, particularly in collaborative environments.
Support Copilots
Customer support teams can utilize iGPT to reconstruct complete customer journeys by analyzing lengthy email chains, attachments, and tone shifts. This comprehensive view allows support agents to provide more personalized and informed assistance to customers.
Insights from Attachments
With iGPT, teams can summarize content from invoices, contracts, and other documents within the context of email threads. This feature enables organizations to extract valuable insights and make data-driven decisions based on comprehensive information.
Threat Watch
Proactive Risk Management
Organizations can utilize Threat Watch to assess their cyber health continuously, enabling proactive measures that can be taken before threats escalate into significant incidents.
Incident Response Coordination
In the event of a detected security breach, Threat Watch facilitates coordinated incident response by providing real-time data and insights, ensuring that all relevant team members are informed and can act swiftly.
Compliance and Reporting
Threat Watch aids organizations in maintaining compliance with industry regulations by providing detailed reports on security posture and breach incidents, making it easier to demonstrate due diligence to stakeholders.
Security Awareness Training
By leveraging the insights from Threat Watch, security teams can educate employees about emerging threats such as phishing attacks and compromised credentials, fostering a culture of awareness and vigilance within the organization.
Overview
About iGPT
iGPT is the ultimate email intelligence API tailored for modern, collaborative enterprises seeking to harness the power of email communication. Designed to be a secure and auditable gateway, iGPT enables teams to develop intelligent, AI-powered systems capable of comprehending and utilizing the rich context inherent in email and communication data. In today's landscape, where email is pivotal for real work, iGPT addresses the critical challenges of fragmentation and inaccessibility that often hinder other AI tools. By transforming chaotic, unstructured email conversations and attachments into reliable, context-aware answers, iGPT streamlines workflows and enhances productivity. Its unified endpoint simplifies the engineering complexities involved in parsing, chunking, indexing, and prompt tuning, allowing development teams to focus on creating impactful workflows and collaborative agents. Ultimately, iGPT empowers organizations to unlock insights from essential communication data while upholding stringent enterprise security and compliance standards.
About Threat Watch
Threat Watch is a cutting-edge unified cybersecurity intelligence platform designed to support and enhance the efforts of your entire security team. It provides a clear, actionable perspective on your organization’s digital risk posture, empowering teams to work collaboratively in safeguarding their assets. This platform serves as a central hub that continuously monitors and analyzes external assets, vulnerabilities, and exposures across various domains, including the clear, deep, and dark web. By aggregating and synthesizing data from these vast sources, Threat Watch generates a comprehensive "cyber health" score. This enables organizations to shift from a reactive approach to a proactive stance in risk management. Tailored for IT leaders, security analysts, and risk management professionals, Threat Watch consolidates data on compromised credentials, devices, phishing campaigns, and dark web threats into one real-time source of truth. Its main value proposition is its ability to foster synergy between different functional teams—from IT operations to executive leadership—ensuring a unified approach to countering threats effectively.
Frequently Asked Questions
iGPT FAQ
What types of businesses can benefit from iGPT?
iGPT is designed for modern enterprises across various sectors that rely heavily on email communication. Teams looking to streamline workflows, enhance productivity, and utilize AI for insights will find significant value in this tool.
How does iGPT ensure data security?
iGPT maintains enterprise-grade protection by implementing zero data training, role-based access control, zero data retention, and a full audit trail. This ensures that user data remains secure and compliant with industry standards.
Can iGPT be integrated with existing systems?
Yes, iGPT is built for easy integration. Its SDK and unified endpoint allow for seamless incorporation into existing workflows and systems, enabling teams to leverage email intelligence without major disruptions.
What is the expected response time from the API?
iGPT delivers impressive performance with around 200 milliseconds for retrieval and approximately 3 seconds to the first token output, even when processing large and complex email data. This responsiveness enhances user experience and workflow efficiency.
Threat Watch FAQ
What types of data does Threat Watch analyze?
Threat Watch analyzes a wide range of data, including information from the clear web, deep web, and dark web. It focuses on external assets, vulnerabilities, and exposures to give a comprehensive view of your organization’s digital risk environment.
How frequently is the information updated on Threat Watch?
Threat Watch updates its information in real-time, ensuring that your security team has access to the latest intelligence on threats, vulnerabilities, and compromised assets as they arise.
Who can benefit from using Threat Watch?
Threat Watch is designed for IT leaders, security analysts, and risk management professionals. Its collaborative nature makes it ideal for teams that need to synchronize their efforts in mitigating risks and responding to threats.
Is Threat Watch suitable for small businesses?
Yes, Threat Watch is suitable for organizations of all sizes. Its comprehensive capabilities allow small businesses to leverage powerful cybersecurity intelligence without the need for extensive resources, enhancing their overall security posture.
Alternatives
iGPT Alternatives
iGPT is a cutting-edge email intelligence API designed for modern enterprises, focusing on transforming messy email data into actionable insights. As organizations increasingly rely on email for communication, users often find themselves seeking alternatives due to various factors, including pricing considerations, specific feature requirements, and compatibility with their existing platforms. The search for an alternative typically hinges on key aspects such as ease of integration, the breadth of functionalities, and the ability to maintain security and compliance standards. When exploring alternatives, it is crucial to evaluate how well they consolidate processes, ease the development burden, and enhance collaboration within teams. Look for solutions that offer a unified approach to data retrieval and reasoning, along with robust indexing capabilities that ensure no critical information is overlooked. The right alternative should empower your team to unlock insights effectively, all while supporting seamless workflows.
Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to assess and strengthen their cybersecurity posture through collaborative insights. As a tool designed for IT leaders, security analysts, and risk management professionals, it provides a comprehensive view of digital risks by continuously analyzing external assets and vulnerabilities. Users often seek alternatives due to various factors such as pricing, specific feature sets, or compatibility with existing platforms. When evaluating alternatives, it's essential to consider aspects like user-friendliness, the breadth of data sources, integration capabilities, and the ability to facilitate teamwork among different security roles. A focus on real-time monitoring and actionable insights can also significantly enhance your organization's cybersecurity effectiveness.