Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right product.
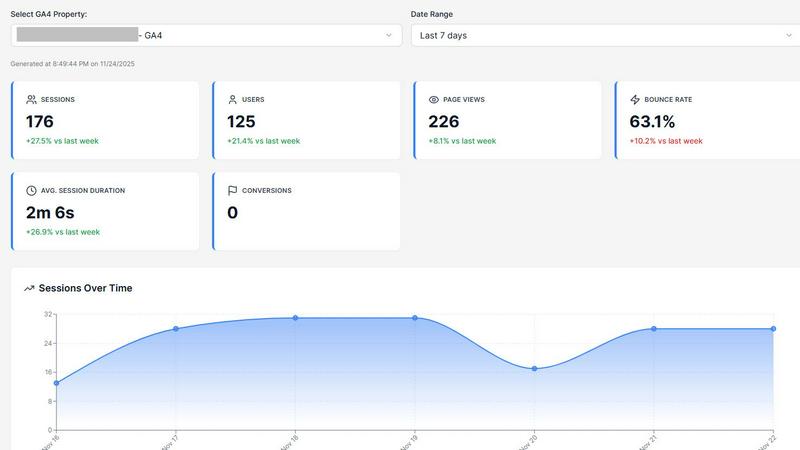
Opal44 simplifies your GA4 website traffic data with AI insights in plain English for smarter, actionable decisions.
Last updated: March 4, 2026
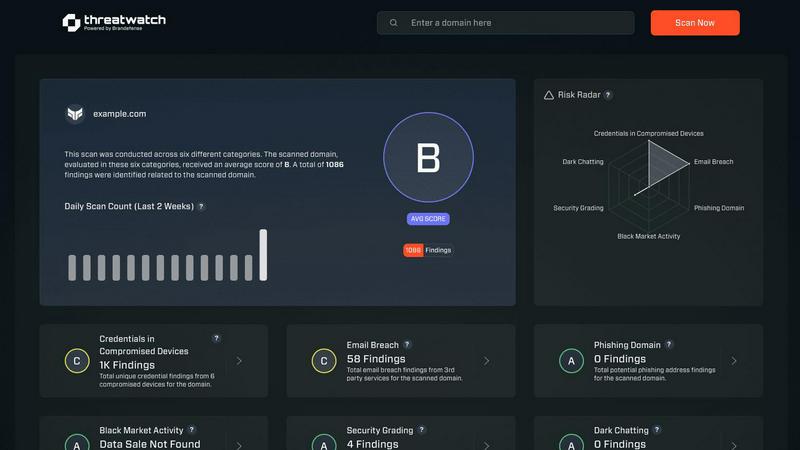
Threat Watch
Collaborate to swiftly evaluate and enhance your team's cybersecurity health with Threat Watch's comprehensive scan.
Last updated: March 1, 2026
Visual Comparison
Opal44
Threat Watch
Feature Comparison
Opal44
Plain English Insights
The AI technology of Opal44 connects directly to your GA4 data, providing insights in simple, everyday language. This feature eliminates the confusion often associated with traditional analytics, allowing users to understand their website performance without any technical expertise.
Conversation-Style Reports
Opal44 presents its analytics in a friendly, conversational format, making it feel as though you're chatting with your own analytics guide. This approach fosters better comprehension and engagement, ensuring that everyone on your team can grasp the insights shared.
Smart, Data-Driven Tips
With tailored recommendations based on your GA4 data, Opal44 provides actionable strategies to enhance website traffic and improve overall performance. These smart tips are designed to help users make data-driven decisions that lead to tangible results.
Real-Time Alerts
Stay ahead of the curve with real-time alerts that notify you of significant changes in your website traffic. Whether it's a spike, drop, or any unusual patterns, Opal44 ensures you're informed immediately, allowing for quick responses to potential issues.
Threat Watch
Comprehensive Cyber Health Scoring
Threat Watch delivers a holistic "cyber health" score that encapsulates your organization's risk posture in real-time, allowing teams to prioritize their security efforts based on data-driven insights.
Real-Time Threat Monitoring
With continuous analysis of assets and vulnerabilities across the internet, Threat Watch provides real-time updates on potential threats, ensuring your security team is always informed and ready to respond swiftly.
Dark Web Surveillance
Threat Watch actively monitors the dark web for leaks and breaches related to your organization, delivering timely alerts that help mitigate risks associated with compromised credentials and sensitive data exposure.
Collaborative Dashboard
The platform features a user-friendly dashboard that promotes collaboration among team members. This centralized view allows IT, security, and executive teams to align their strategies and responses based on a unified understanding of threats.
Use Cases
Opal44
Small Business Analytics
Small business owners can utilize Opal44 to easily understand their website traffic and performance without requiring a background in analytics. This enables them to optimize their online presence effectively.
Marketing Campaign Tracking
Marketing teams can leverage Opal44 to track the success of their campaigns. The plain English insights and real-time alerts help assess performance and make necessary adjustments on the fly.
E-commerce Optimization
E-commerce managers can use Opal44 to gain insights into customer behavior and website performance. By understanding traffic patterns, they can implement strategies to enhance conversions and customer engagement.
Client Reporting for Agencies
Digital agencies can benefit from Opal44’s clear reporting features. The conversation-style reports make it easier to present insights to clients, ensuring productive strategy meetings and better client relationships.
Threat Watch
Proactive Risk Management
Organizations can utilize Threat Watch to assess their cyber health continuously, enabling proactive measures that can be taken before threats escalate into significant incidents.
Incident Response Coordination
In the event of a detected security breach, Threat Watch facilitates coordinated incident response by providing real-time data and insights, ensuring that all relevant team members are informed and can act swiftly.
Compliance and Reporting
Threat Watch aids organizations in maintaining compliance with industry regulations by providing detailed reports on security posture and breach incidents, making it easier to demonstrate due diligence to stakeholders.
Security Awareness Training
By leveraging the insights from Threat Watch, security teams can educate employees about emerging threats such as phishing attacks and compromised credentials, fostering a culture of awareness and vigilance within the organization.
Overview
About Opal44
Opal44 is an innovative analytics tool designed to simplify the often-complex world of website traffic insights. By leveraging AI technology, Opal44 connects seamlessly with Google Analytics 4 (GA4) to provide users with clear and actionable insights about their website performance. Whether you're a small business owner, a digital marketer, or part of a larger organization, Opal44 is crafted for anyone who seeks to understand their web traffic without getting lost in jargon or complicated metrics. Its primary value proposition lies in transforming raw data into plain English, making analytics accessible and comprehensible for all users. With features such as real-time alerts, conversation-style reports, and tailored recommendations, Opal44 empowers users to make informed decisions swiftly. Join countless businesses worldwide that are already experiencing the benefits of simplified web analytics.
About Threat Watch
Threat Watch is a cutting-edge unified cybersecurity intelligence platform designed to support and enhance the efforts of your entire security team. It provides a clear, actionable perspective on your organization’s digital risk posture, empowering teams to work collaboratively in safeguarding their assets. This platform serves as a central hub that continuously monitors and analyzes external assets, vulnerabilities, and exposures across various domains, including the clear, deep, and dark web. By aggregating and synthesizing data from these vast sources, Threat Watch generates a comprehensive "cyber health" score. This enables organizations to shift from a reactive approach to a proactive stance in risk management. Tailored for IT leaders, security analysts, and risk management professionals, Threat Watch consolidates data on compromised credentials, devices, phishing campaigns, and dark web threats into one real-time source of truth. Its main value proposition is its ability to foster synergy between different functional teams—from IT operations to executive leadership—ensuring a unified approach to countering threats effectively.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 connect to my Google Analytics 4 account?
Opal44 offers a quick and secure setup process that requires no coding. Simply follow the prompts to connect your GA4 account, and you can start receiving insights within minutes.
Is my data safe with Opal44?
Absolutely. Opal44 prioritizes your data privacy and security, ensuring that your GA4 information remains confidential. We never sell or share your data with third parties.
What kind of support can I expect as a user?
Opal44 provides excellent customer support, including email assistance and priority support for higher-tier plans. Our dedicated team is ready to help you with any questions or issues you may encounter.
Can I cancel my subscription at any time?
Yes, Opal44 offers a flexible subscription model with no setup fees and the ability to cancel at any time. This means you can try our services risk-free.
Threat Watch FAQ
What types of data does Threat Watch analyze?
Threat Watch analyzes a wide range of data, including information from the clear web, deep web, and dark web. It focuses on external assets, vulnerabilities, and exposures to give a comprehensive view of your organization’s digital risk environment.
How frequently is the information updated on Threat Watch?
Threat Watch updates its information in real-time, ensuring that your security team has access to the latest intelligence on threats, vulnerabilities, and compromised assets as they arise.
Who can benefit from using Threat Watch?
Threat Watch is designed for IT leaders, security analysts, and risk management professionals. Its collaborative nature makes it ideal for teams that need to synchronize their efforts in mitigating risks and responding to threats.
Is Threat Watch suitable for small businesses?
Yes, Threat Watch is suitable for organizations of all sizes. Its comprehensive capabilities allow small businesses to leverage powerful cybersecurity intelligence without the need for extensive resources, enhancing their overall security posture.
Alternatives
Opal44 Alternatives
Opal44 is an innovative tool designed for business intelligence, offering AI-powered insights into website traffic through an intuitive interface that eliminates jargon. By utilizing Google Analytics 4, it helps users gain a clearer understanding of their data, making it easier to take actionable steps for improvement. This product appeals to businesses looking to enhance their online performance through data-driven decisions. However, users may seek alternatives to Opal44 for various reasons, such as pricing, specific feature sets, or compatibility with different platforms. When exploring alternatives, it’s essential to consider factors like ease of use, the comprehensiveness of insights provided, and the level of customer support available. A collaborative approach in selecting the right tool can also ensure that it meets the diverse needs of your team and aligns with your business objectives.
Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to assess and strengthen their cybersecurity posture through collaborative insights. As a tool designed for IT leaders, security analysts, and risk management professionals, it provides a comprehensive view of digital risks by continuously analyzing external assets and vulnerabilities. Users often seek alternatives due to various factors such as pricing, specific feature sets, or compatibility with existing platforms. When evaluating alternatives, it's essential to consider aspects like user-friendliness, the breadth of data sources, integration capabilities, and the ability to facilitate teamwork among different security roles. A focus on real-time monitoring and actionable insights can also significantly enhance your organization's cybersecurity effectiveness.