Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
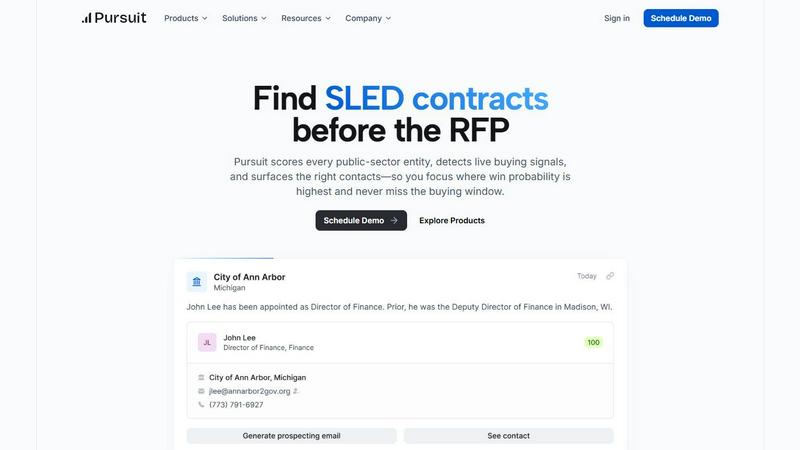
Pursuit
Pursuit empowers teams to uncover public sector opportunities early, ensuring they connect and win before RFPs are.
Last updated: February 28, 2026
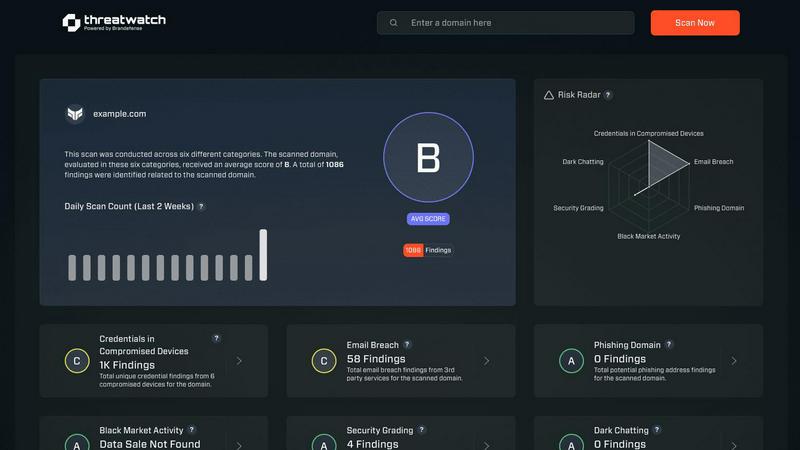
Threat Watch
Collaborate to swiftly evaluate and enhance your team's cybersecurity health with Threat Watch's comprehensive scan.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Early Buying Signal Detection
Pursuit identifies crucial buying signals 6 to 18 months before RFPs are released. This proactive approach allows your team to position themselves as incumbents rather than outsiders, ensuring they have a competitive edge.
Comprehensive Data Insights
The platform aggregates data from various sources, including council meetings and budget documents, to unearth hidden signals. This intelligence provides teams with the insights needed to navigate complex procurement processes effectively.
Native Integrations
Pursuit seamlessly integrates with existing CRM systems like Salesforce and HubSpot. This data flow eliminates the need for extensive engineering work, allowing your teams to focus on strategy and execution.
Role-Specific Functionality
Designed with every role in mind, Pursuit offers tailored tools for revenue operations, sales leaders, marketing teams, account executives, and customer success managers. Each function benefits from deep, specific capabilities that enhance their respective workflows.
Threat Watch
Comprehensive Cyber Health Scoring
Threat Watch delivers a holistic "cyber health" score that encapsulates your organization's risk posture in real-time, allowing teams to prioritize their security efforts based on data-driven insights.
Real-Time Threat Monitoring
With continuous analysis of assets and vulnerabilities across the internet, Threat Watch provides real-time updates on potential threats, ensuring your security team is always informed and ready to respond swiftly.
Dark Web Surveillance
Threat Watch actively monitors the dark web for leaks and breaches related to your organization, delivering timely alerts that help mitigate risks associated with compromised credentials and sensitive data exposure.
Collaborative Dashboard
The platform features a user-friendly dashboard that promotes collaboration among team members. This centralized view allows IT, security, and executive teams to align their strategies and responses based on a unified understanding of threats.
Use Cases
Pursuit
Effective Lead Prioritization
Sales development representatives (SDRs) can leverage Pursuit's daily prioritized call lists based on real-time buying signals. This feature eliminates guesswork, allowing for more strategic outreach to high-potential leads.
Improved Renewal Management
Customer success teams can set up alerts for upcoming contract renewals, ensuring they proactively address potential churn signals. This foresight enables teams to maintain strong relationships and minimize customer turnover.
Enhanced Account-Based Marketing
Marketing teams can craft targeted ABM campaigns that align with real buying signals, such as budget approvals and contract expirations. This approach increases campaign effectiveness and conversion rates significantly.
Informed Sales Conversations
Account executives benefit from Pursuit's Chrome extension, which provides instant access to essential account intelligence before meetings. This capability ensures they are well-prepared for every customer interaction, enhancing their chances of closing deals.
Threat Watch
Proactive Risk Management
Organizations can utilize Threat Watch to assess their cyber health continuously, enabling proactive measures that can be taken before threats escalate into significant incidents.
Incident Response Coordination
In the event of a detected security breach, Threat Watch facilitates coordinated incident response by providing real-time data and insights, ensuring that all relevant team members are informed and can act swiftly.
Compliance and Reporting
Threat Watch aids organizations in maintaining compliance with industry regulations by providing detailed reports on security posture and breach incidents, making it easier to demonstrate due diligence to stakeholders.
Security Awareness Training
By leveraging the insights from Threat Watch, security teams can educate employees about emerging threats such as phishing attacks and compromised credentials, fostering a culture of awareness and vigilance within the organization.
Overview
About Pursuit
Pursuit is a cutting-edge platform specifically designed to enhance the sales process for businesses engaging with public-sector entities. It empowers organizations such as government contractors, vendors, and service providers to strategically navigate the complexities of selling to the public sector. By providing advanced scoring for over 110,000 public-sector organizations and identifying live buying signals, Pursuit enables sales teams to prioritize opportunities with the highest probability of success. This comprehensive tool not only surfaces key contacts but also ensures that sales teams are prepared to engage with potential clients at the right time, leveraging AI-driven insights and data. The main value proposition lies in its ability to streamline the sales process, reduce research time, and ultimately, increase win rates in a market known for its unique challenges.
About Threat Watch
Threat Watch is a cutting-edge unified cybersecurity intelligence platform designed to support and enhance the efforts of your entire security team. It provides a clear, actionable perspective on your organization’s digital risk posture, empowering teams to work collaboratively in safeguarding their assets. This platform serves as a central hub that continuously monitors and analyzes external assets, vulnerabilities, and exposures across various domains, including the clear, deep, and dark web. By aggregating and synthesizing data from these vast sources, Threat Watch generates a comprehensive "cyber health" score. This enables organizations to shift from a reactive approach to a proactive stance in risk management. Tailored for IT leaders, security analysts, and risk management professionals, Threat Watch consolidates data on compromised credentials, devices, phishing campaigns, and dark web threats into one real-time source of truth. Its main value proposition is its ability to foster synergy between different functional teams—from IT operations to executive leadership—ensuring a unified approach to countering threats effectively.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit help with the complexities of SLED sales?
Pursuit streamlines the SLED sales process by identifying key buying signals well in advance of RFPs. It aggregates critical data and insights, allowing teams to navigate the unique procurement rules and budget cycles effectively.
Can Pursuit integrate with my existing tools?
Yes, Pursuit offers native integrations with popular CRM platforms like Salesforce and HubSpot. This ensures that your data flows seamlessly, enhancing collaboration without requiring extensive engineering resources.
What kind of support does Pursuit offer?
Pursuit provides comprehensive resources, including case studies and demo scheduling options, to ensure that users can maximize the platform's capabilities. Support is tailored to help teams at all stages of their sales process.
How does Pursuit improve team collaboration?
By sharing intelligence across your go-to-market team, Pursuit fosters collaboration among marketing, sales, and customer success teams. When everyone has access to the same insights, signals flow seamlessly from awareness to deal closure.
Threat Watch FAQ
What types of data does Threat Watch analyze?
Threat Watch analyzes a wide range of data, including information from the clear web, deep web, and dark web. It focuses on external assets, vulnerabilities, and exposures to give a comprehensive view of your organization’s digital risk environment.
How frequently is the information updated on Threat Watch?
Threat Watch updates its information in real-time, ensuring that your security team has access to the latest intelligence on threats, vulnerabilities, and compromised assets as they arise.
Who can benefit from using Threat Watch?
Threat Watch is designed for IT leaders, security analysts, and risk management professionals. Its collaborative nature makes it ideal for teams that need to synchronize their efforts in mitigating risks and responding to threats.
Is Threat Watch suitable for small businesses?
Yes, Threat Watch is suitable for organizations of all sizes. Its comprehensive capabilities allow small businesses to leverage powerful cybersecurity intelligence without the need for extensive resources, enhancing their overall security posture.
Alternatives
Pursuit Alternatives
Pursuit is an innovative solution within the business intelligence category, designed to help organizations identify and connect with public sector opportunities effectively. By utilizing comprehensive data and AI-driven insights, Pursuit enables businesses, including government contractors and service providers, to maximize their revenue potential in a competitive landscape. Users often seek alternatives to Pursuit for various reasons, such as pricing considerations, specific feature requirements, or the need for compatibility with existing platforms. When evaluating alternatives, it’s essential to consider factors such as the comprehensiveness of data, the usability of the interface, integration capabilities, and the overall value provided to ensure that the chosen solution aligns well with your organization’s strategic goals.
Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to assess and strengthen their cybersecurity posture through collaborative insights. As a tool designed for IT leaders, security analysts, and risk management professionals, it provides a comprehensive view of digital risks by continuously analyzing external assets and vulnerabilities. Users often seek alternatives due to various factors such as pricing, specific feature sets, or compatibility with existing platforms. When evaluating alternatives, it's essential to consider aspects like user-friendliness, the breadth of data sources, integration capabilities, and the ability to facilitate teamwork among different security roles. A focus on real-time monitoring and actionable insights can also significantly enhance your organization's cybersecurity effectiveness.