AutoPhish vs CMMC ROI
Side-by-side comparison to help you choose the right product.
AutoPhish empowers teams with AI-driven phishing simulations and tailored training to enhance security awareness.
Last updated: March 1, 2026
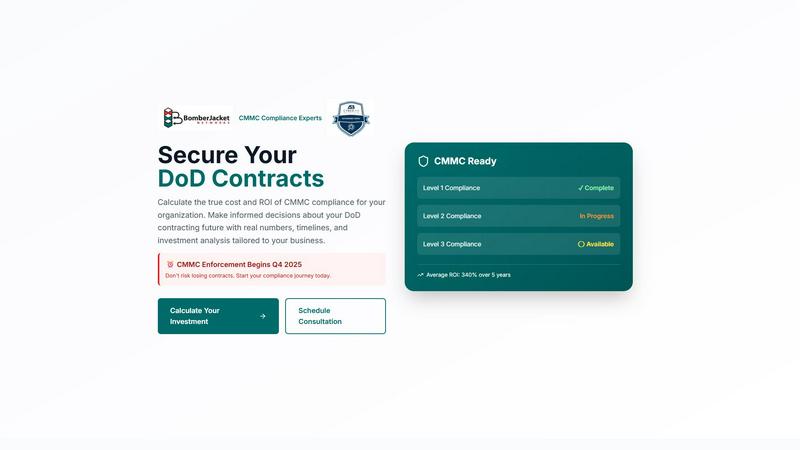
CMMC ROI
Calculate your CMMC compliance ROI together to secure DoD contracts with confidence.
Last updated: March 1, 2026
Visual Comparison
AutoPhish
CMMC ROI
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish utilizes advanced AI technology to create phishing emails that closely mimic actual attacks, tailored specifically to your industry. This ensures that your team encounters scenarios they are likely to face in the real world, enhancing their preparedness and response capabilities.
Automated Campaigns
With the automated campaigns feature, organizations can schedule and run phishing tests without manual intervention. This not only saves time but also facilitates consistent training, allowing your team to stay vigilant against phishing threats without overwhelming your resources.
Targeted Training
AutoPhish offers targeted training modules that adapt based on the results of phishing simulations and individual user roles. This personalized approach helps in addressing specific vulnerabilities and ensures that employees receive the most relevant training to enhance their cybersecurity awareness.
Comprehensive Reporting
The platform provides advanced reporting features that allow organizations to analyze the results of phishing simulations in detail. This includes insights into user performance, identifying at-risk individuals, and tracking progress over time, which helps in refining training strategies and assessing overall cybersecurity readiness.
CMMC ROI
Personalized ROI Calculator
Our core interactive calculator allows your team to input your specific company data—size, DoD revenue, target CMMC level, and current progress—to generate a tailored financial model. It provides a clear range for your 5-year total investment, projected ROI percentage, and the precise month you'll break even, turning abstract compliance costs into a tangible business case for your entire organization to rally behind.
Scenario-Based Investment Modeling
Jumpstart your planning with pre-loaded scenarios for common contractor profiles, from small FCI handlers to large prime contractors. These quick examples provide immediate ballpark figures, fostering productive internal discussions. For a truly collaborative strategy, you can then seamlessly modify any assumption to reflect your unique operational environment and see the results update in real-time.
Visual Timeline and Milestone Tracker
Achieving certification is a team journey. Our tool outlines a detailed, 12-month implementation roadmap to CMMC Level 2, breaking the process into clear phases like Gap Assessment, Remediation, and Documentation. This shared visual plan helps synchronize efforts across IT, security, and management, setting realistic expectations and celebrating collective progress at each milestone.
Executive Briefing and Risk Assessment
Translate technical compliance into executive language with a downloadable briefing that summarizes your calculated ROI, protected contract value, and key risk metrics. It clearly quantifies the 100% contract loss risk without certification and the significant cost of avoided breaches, providing a powerful, unified narrative to secure buy-in and resources from all stakeholders.
Use Cases
AutoPhish
Cybersecurity Training for Employees
Organizations can use AutoPhish to deliver engaging and relevant cybersecurity training to employees. By simulating real-world phishing attacks, employees can learn how to recognize and respond to threats effectively, fostering a security-conscious culture.
Vulnerability Assessment
AutoPhish serves as a powerful tool for conducting vulnerability assessments within organizations. By identifying at-risk users through simulated attacks, companies can focus their training efforts on those who need it most, thus strengthening their overall security posture.
Industry-Specific Training
Different industries face unique phishing threats. AutoPhish’s ability to tailor simulations to specific sectors allows businesses to provide industry-relevant training, ensuring employees are equipped to handle the specific challenges they may encounter.
Continuous Improvement of Security Protocols
AutoPhish enables organizations to continuously improve their security protocols by regularly testing and training employees. This iterative approach ensures that as phishing tactics evolve, so does the organization's readiness and defense mechanisms against potential attacks.
CMMC ROI
Securing Leadership and Budget Approval
Finance and executive teams often see compliance as a pure cost. Use CMMC ROI to build a compelling, numbers-driven business case that demonstrates a positive return on investment, a clear payback period, and the severe financial risk of non-compliance. This collaborative approach aligns leadership on the strategic necessity of funding the certification journey.
Strategic Planning for Business Development
Business development and proposal teams can leverage the tool to understand how CMMC certification impacts bid strategies and win rates. By quantifying the "contract value at risk" and the competitive advantage, your organization can confidently pursue larger or more strategic DoD contracts, knowing your compliance posture is a key differentiator.
Prioritizing and Phasing Compliance Efforts
For IT and security teams starting from scratch, the detailed cost breakdown and implementation timeline provide a framework for collaborative planning. It helps prioritize which security controls to implement first based on impact and cost, allowing for a phased, manageable approach that aligns technical work with business readiness and budget cycles.
Evaluating Compliance Service Providers
When engaging with C3PAOs or Managed Service Providers, use your personalized CMMC ROI report as a benchmark. It provides an independent, data-backed estimate for implementation and maintenance costs, empowering your team to have more informed, collaborative negotiations and select a partner whose proposal aligns with your financial model.
Overview
About AutoPhish
AutoPhish is an innovative AI-powered platform designed to bolster organizational cybersecurity through realistic phishing simulations and tailored security awareness training. Aimed at businesses of all sizes, AutoPhish enables teams to proactively identify and mitigate potential vulnerabilities before malicious actors can exploit them. By simulating real-world phishing attacks that are customized to specific industries, AutoPhish provides employees with relevant and practical training experiences. The platform's automated campaign feature allows organizations to effortlessly schedule and execute phishing tests, ensuring consistent training while conserving valuable resources. With adaptive training modules based on simulation outcomes and user roles, AutoPhish cultivates a culture of security awareness, empowering teams with the knowledge and skills necessary to effectively combat evolving cyber threats.
About CMMC ROI
CMMC ROI is a strategic, data-driven platform from BomberJacket Networks, an authorized C3PAO, designed to transform the CMMC compliance journey from a perceived cost center into a clear, quantifiable business investment. It is built for Department of Defense (DoD) contractors of all sizes who need to understand the true financial impact of achieving and maintaining CMMC certification. With enforcement set to begin in Q4 2025, the risk of inaction is total contract loss. This tool moves the conversation beyond technical checklists, empowering leadership teams to collaborate on a compliance strategy grounded in real numbers. By calculating a personalized 5-year ROI, implementation timeline, and payback period, CMMC ROI enables organizations to make informed, confident decisions about their future in the defense industrial base. It aligns cybersecurity efforts with business objectives, ensuring your investment not only secures contracts but also enhances your competitive edge and protects your revenue stream.
Frequently Asked Questions
AutoPhish FAQ
What types of phishing simulations does AutoPhish offer?
AutoPhish provides a range of phishing simulations that mimic real-world email attacks, tailored to specific industries and organizational needs. This ensures that employees encounter realistic scenarios that enhance their preparedness.
How does AutoPhish help in training employees?
AutoPhish helps train employees by providing targeted training modules based on the outcomes of phishing simulations. This personalized approach focuses on addressing specific vulnerabilities, making training more effective.
Can I automate phishing tests with AutoPhish?
Yes, AutoPhish features automated campaigns that allow organizations to schedule and run phishing tests without manual intervention. This feature ensures consistent training and maintains vigilance against phishing threats.
How does AutoPhish report on simulation results?
AutoPhish offers comprehensive reporting tools that analyze the results of phishing simulations. Organizations can track user performance, identify at-risk individuals, and monitor overall cybersecurity readiness, aiding in the refinement of training strategies.
CMMC ROI FAQ
How accurate is the ROI calculation?
Our calculations are based on industry-standard cost ranges for CMMC implementation, maintenance, and recertification, refined by BomberJacket Networks' 20+ years of direct experience. While individual results may vary, the model uses your specific inputs—like company size, revenue, and progress discounts—to provide a highly reliable financial projection for strategic planning and stakeholder alignment.
What is included in the "Protected Value" for the ROI formula?
The Protected Value is a collaborative estimate of what CMMC certification safeguards. It combines your organization's 5-year DoD contract revenue (which is 100% at risk without certification) with an industry-average cost avoidance for a potential data breach or False Claims Act violation, typically set at $2.5 million. This holistic view captures both revenue protection and risk mitigation.
My company is already working on compliance. Can the tool still help?
Absolutely. By selecting your "Current Compliance Status" as "In Progress" or "Nearly Complete," the calculator applies significant discounts (30% or 60%) to the implementation cost. This allows your team to model the remaining investment required to reach certification, providing a clear picture of the final push needed and its associated return, fostering momentum.
When should we start our CMMC compliance journey?
With enforcement beginning in Q4 2025, the time for collaborative action is now. Our model shows a typical Level 2 certification journey takes about 12 months. Starting early allows your team to approach the process strategically, phase costs, and avoid rushed, expensive last-minute efforts. It ensures you are ready to bid when certified contracts are released.
Alternatives
AutoPhish Alternatives
AutoPhish is a cutting-edge platform designed to enhance organizational cybersecurity through AI-driven phishing simulations and tailored training. As part of the Business Intelligence and Productivity & Management categories, it empowers teams to proactively identify vulnerabilities and cultivate a culture of security awareness. Users often seek alternatives to AutoPhish for various reasons, including pricing, feature set, or compatibility with specific organizational needs. When choosing an alternative, it's essential to evaluate the platform's training capabilities, simulation realism, and the flexibility to adapt to your team's unique requirements.
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence tool designed to help defense contractors calculate the financial return on investment for achieving Cybersecurity Maturity Model Certification (CMMC). It provides data-driven insights to guide strategic planning and investment for securing Department of Defense contracts. Teams often explore alternatives to find a solution that best fits their specific operational needs and budget. This could be due to differences in pricing models, the need for integration with existing project management platforms, or a desire for different feature sets like more granular reporting or collaborative workflow tools. When evaluating different options, it's wise for a team to prioritize solutions that offer clear, actionable data and foster a collaborative approach to compliance. The ideal tool should not only provide accurate ROI projections but also seamlessly integrate into your team's existing processes, enabling synergy between your cybersecurity, finance, and business development units to streamline the path to certification.

